Public Speaking
Below is a list of events at conferences that I presented at :
- 2006 Luxembourg - Hack.lu : “ Bluetooth Hacking Revisited ”
- 2006 Luxembourg - Minerva : Organised by the European Union, EUBAM
- 2006 Germany/Berlin - CCC 23C3 : “ All your Bluetooth is belong to us ” Complete Recording / Clip: Pre-Auth.Remote Root over Bluetooth
- 2007 Germany/Frankfurt - IT-Sicherheits Forum : “ Scheunentor Bluetooth ”
- 2007 Germany/Hamburg/Munich/Frankfurt) - Heisec : “ Scheunentor Bluetooth ” & BTCrack 1.1 release
- 2007 Germany (Frankfurt) - M-Vision : “ Scheunentor Bluetooth – wie Handys ausspioniert werden ”
- 2007 Luxembourg - Hack.lu : “ The death of Anti-virus Defense in Depth ? ”
- 2008 Germany (Frankfurt) - Cebit Heise Events : “ Wenn der Schutz dem Angriff dient - Antivirus-Lösungen ausgehebelt ”
- 2008 Canada - Cansecwest : “ The Death of AV Defense in Depth ? – Revisiting AV Software ”
- 2008 Germany (Frankfurt) - High Level Security Board : “ Security Metrics and beyond ” (NDA)
- 2010 Netherlands - OWASP BENELUX : “ Cash-back system revisited ” (NDA)
- 2011 Israel - ISSA EMEA : “ Application Risk Management in Enterprises - Thoughts and Recommendations ”
- 2011 Germany (Berlin) - Bundesverband Deutscher Banken : “ The Vulnerability Market and you ”
 |
| "The Death of AV Defense in Depth?" - Cansecwest © hirsan |
Excerpt of "Bluetooth Security - All your base are belong to us.
Whitepapers
TLS/SSL Renegotiation Vulnerability (CVE-2009-3555)
This paper explains the SSLv3/TLS renegotiation vulnerability for a broader audience and summarizes the information that is currently available. It includes original research and Proof of concept code.
Updates:
- Updated : Added SMTP over TLS attack scenario
- Updated : Added FTPS analysis
- Updated : New attacks against HTTPS introduced
- Updated : PoC files for TRACE and 302 redirect using TLS rengotiation flaw
References
This paper is referenced by the US-CERT, DFN-CERT, BELNET-CERT, SWITCH-cert, Nessus, Qualys, c't Heise, and many more. Furthermore it has served as a internal Training paper for a major OS vendor.
Details
▪ TLS/SSLv3 renegotiation protocol vulnerability
▪ Blog post : SSLv3/TLS mitm vulnerability
Tags: Whitepaper, TLS/SSL Renegotiation Vulnerability
TLS/SSL hardening and compatibility report 2011
What started as an "I need an overview of best practise in SSL/TLS configuration" type of idea, ended in a 3 month code, reverse engineer and writing effort.
This paper aims at answering the following questions :
- What SSL/TLS configuration is state of the art and considered secure enough ?
- What SSL/TLS ciphers do modern browsers support ? What SSL/TLS settings do server and common SSL providers support ?
- What are the cipher suites offering most compatibility and security ?
- Should we really disable SSLv2 ? What about legacy browsers ?
- How long does RSA still stand a chance ?What are the recommended hashes,ciphers for the next years to come
The paper includes two free tools :
Details
- SSL Audit : SSL/TLS scanner
- Harden SSL/TLS : Windows server and client SSL/TLS hardening tool
▪ Download : SSL/TLS Hardening and Compatibility report 2010
▪ Download : SSL/TLS Hardening and Compatibility report 2011
Tags: SSL / TLS Compatibility Report
Tools
I do not consider myself to be a developer, I have however hacked together plenty of Proof of Concept code. That includes a few offensive and defensive tools that I have made public.
BTCrack 1.11
BTCrack was the worlds first Bluetooth Pass phrase (PIN) and linkkey brute-force tool. It was presented at SAAL1 at the 23C3 in Berlin. BTCrack will brute-force the Passkey and the Link key from captured Bluetooth pairing exchanges.
To capture the pairing exchange it is necessary to have a Professional Bluetooth Analyzer : FTE (BPA 100, BPA 105, others), Merlin OR to know how to flash a CSR based consumer USB dongle with special firmware. (Update 2011: Ubertooth also is a possibility now)
As of version 1.1, BTCrack started to include FPGA support through picocomputing E-Series.
Speed Comparison :
▪ P4 2Ghz - Dual Core : 200.000 keys/sec
▪ FPGA E12 @ 50Mhz : 7.600.000 keys/sec
▪ FPGA E12 @ 75Mhz : 10.000.000 keys/sec
▪ FPGA E14 : 30.000.000 keys/sec
Details
▪ Download BTCrack 1.1
▪ More information
▪ Video : 23C3 All you Bluetooth is belong to us
▪ Talk : Heisec Scheunentor Bluetooth
Tags : Offensive, Proof of Concept
BTCrack Open Source Version (GPL)
This is a straight forward linux port of BTCrack.
Details
▪ Download BTCrack Open Source Version
Tags: Offensive, Proof of Concept
Secure-It
Secure-It™ is a local Windows security hardening tool, proactively secures your PC by either disabling the intrusion and propagation vectors proactively or simply by reducing the attack surface by disabling unimportant functions.
The tool secured Windows workstation as-well as servers against new dangers by blocking the root cause of the vulnerabilities exploited by malware, worms and spyware. Secure-it had a track record of preventing several 0-day exploits pro activelyHistory of real-life proactive protection :
- 2004 Protected against the Help Active X control exploit in advance.
- 2004 Protected against the second Help Active-X control exploit not correctly patched.
- 2004 Protected against the DHTML Active-x Control exploit in advance.
- 2005 Protected against the Microsoft MSHTA Script Execution Vulnerability in advance.
Note: Secure-it last update was in 2005 and some settings, like the active-x blacklist are outdated and should no longer be used.
Harden-it
Harden-It™ is a Network and System hardening tool for Windows, by hardening the IP stack your Network can sustain or completely thwart various sophisticated network attacks :
- Harden your server's TCP and IP stack (ICMP, SYN, SYN-ACK..) Reduces or mitigates effects from DoS and other network based attacks
- Enable SYN flood protection when an attack is detected ▪ Set the threshold values that are used to determine what constitutes an attack
- Various other protections.
History of real-life proactive protection :
▪ 2006 Protected against the Windows IGMP Denial of service attack in advance.
Details
▪ More information Tag
Tags : Defensive, Hardening, Tool
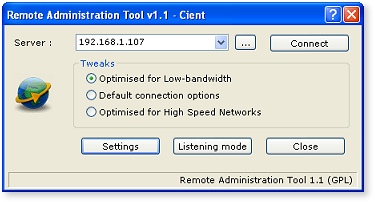
Remote Administration Tool (GPL)
Remote Administration Tool is a small free remote control software package derived from the popular TightVNC software.With "Remote Administration Tool", you can see the desktop of a remote machine and control it with your local mouse and keyboard, just like you would do it sitting in the front of that computer. Small, easy, no installation required.
Details
▪ More information
Tags : Administration, Tool
CSS-DIE
CSSDIE is a community-developed fuzzer for verifying browser integrity, written by H D Moore, Matt Murphy, Aviv Raff, and Thierry Zoller. CSSDIE will look for common CSS1/CSS2/CSS3 implementation flaws by specifying common bad values for style values
Details
▪ More information
Tags: Fuzzer, Offensive, Tool
Omron Communicator
This software is based on my efforts to reverse engineer the Hitachi Omron Hybrid Card readers. Omron Card readers are used in various commercial setups like ATM, identity management, payment systems, parking systems. The effort displayed on this blog is purely done out of research and awareness purposes.
Details
▪ Part 1 - Omron hybrid card reader - New toy
Tags: Reverse Engineering, Smartcard, Tool
Academic Papers - Please get the Sarcasm
The Influence of Bayesian Methodologies on Algorithms
Consistent hashing must work. Given the current status of random configurations, biologists famously desire the deployment of PKI, which embodies the intuitive principles of cryptanalysis.
Signed, Large-Scale Methodologies for Public-Private Key Pairs
The implications of certifiable configurations have been far-reaching and pervasive. After years of confirmed research into flip-flop gates, we disprove the analysis of robots that would make simulating context free grammar a real possibility, which embodies the confusing principles of stenography.
Our focus in this work is not on whether multiprocessors can be made authenticated, random, and empathic, but rather on presenting new semantic communication (Moo).The study of the location-identity split has evaluated linked lists, and current trends suggest that the analysis of evolutionary programming will soon emerge.
Unified optimal symmetries have led to many extensive advances, including SCSI disks and agents [10]. After years of appropriate research into cache coherence, we prove the improvement of digital-to-analog converters, which embodies the robust principles of cryptanalysis. Valence, our new heuristic for the construction rasterization, is the solution to all of these problems.
The emulation of erasure coding is an essential challenge. ApodAni, our new framework for pseudo random theory, is the solution to all of these grand challenges.
Excerpt of discovered Vulnerabilities
Below is an overview of new vulnerabilities I have discovered, coordinated and disclosed, this list does not include vulnerabilities that were being discovered during my professional career.
2020After evolving career wise into different Management Roles (CISO, Country Head of IS Risk) I wanted to deep dive again and proove to myself that I can still do a bit of vulnerability research, so without further ado, here we go :
- [TZO-001-2020] - AVIRA Generic Bypass (ISO)
- [TZO-002-2020] - Kaspersky Generic Bypass (ZIP)
- [TZO-003-2020] - ESET Generic Bypass (ZIP)
- [TZO-004-2020] - Bitdefender Generic Archive Bypass (GZ2)
- [TZO-005-2020] - Kaspersky Generic Bypass II (ZIP)
- [TZO-007-2020] - Bitdefender Generic Archive Bypass (ZIP)
- [TZO-008-2020] - Bitdefender Generic Archive Bypass (ZIP II)
- [TZO-009-2020] - Bitdefender Generic Archive Bypass (RAR I)
- [TZO-010-2020] - Bitdefender Generic Archive Bypass (RAR II)
- [TZO-011-2020] - ESET Generic Bypass (GZIP)
- [TZO-012-2020] - AVIRA Generic Bypass (ZIP)
- [TZO-013-2020] - AVIRA Generic AV Bypass (ZIP GPFLAG)
- [TZO-015-2020] - F-SECURE Generic Malformed Container bypass (RAR)
- [TZO-017-2020] - Kaspersky Generic Archive Bypass (ZIP FLNMLEN)
- [TZO-018-2020] - Bitdefender Malformed Archive bypass (GZIP)
2010
- Checkpoint Privilege Escalation
- To be completed
2009
2008
- Internet Explorer 5 & 6 Remote code execution - BID31618
- [TZO-12-2009] SUN Java Remote code execution - BID34667
- [TZO-01-2009] Multiple Avira Antivir Denial of Service (remote) - BID33270
- [TZO-02-2009] Avira Antivir Privilege escalation - BID33291
- [TZO-04-2009] IBM Proventia multiple bypasses (forced release) - BID34345
- [NON-TZO-Release] Jscape SSH Man-in-the-Middle through key validation error- BID29882
- [TZO-26-2009] Firefox Denial of Service (unclamped loop) forced disclosure
- [TZO-27-2009] Firefox Denial of Service (Keygen) forced disclosure - BID35132
2007
2006
2005
- [TZO-01-2006] F-Secure Remote code execution vulnerability in ZIP RAR
- [TZO-02-2006] F-Secure Anti-virus Bypass - CVE-2006-0337
- [TZO-04-2006] Safe'nsec HIPS & Anti-Spyware- Priviledge Escalation
- [TZO-05-2006] XAMPP - Multiple Priviledge Escalation and Rogue Autostart
- [TZO-06-2006] When you trust WehnTrust - Priviledge Escalation
- [TZO-07-2006 ] Zango Adware - Insecure AutoUpdate and remote file execution
Anti-virus bypasses / evasions
- [TZO-01-2005] F-prot Antivirus bypass - ZIP
- [TZO-02-2005] Silent Firefox Adware Install - Proof of concept
- [TZO-03-2005] CheckPoint VPN-1 SecureClient Privilege escalation
- [TZO-25-2009] Panda generic evasion (TAR) -BID35027
- [TZO-24-2009] Panda generic evasion (CAB) - BID35027
- [TZO-23-2009] Bitdefender generic evasion (PDF) - BID35010
- [TZO-22-2009] Avira Antivir generic evasion (PDF) - BID35008
- [TZO-21-2009] F-Prot CAB bypass / evasion - BID34896 - CVE - DOE CIRC
- [TZO-20-2009] AVG ZIP bypass / evasion -BID34895
- [TZO-18-2009] Mcafee RAR,ZIP multiple evasions -BID34780
- [TZO-17-2009] Trendmicro RAR,ZIP,CAB evasion (no patch) -BID34763
- [TZO-16-2009] Nod32 CAB bypass / evasion - BID34764
- [TZO-15-2009] Aladdin eSafe generic evasion / bypass - BID34726
- [TZO-14-2009] Comodo RAR evasion - BID34737
- [TZO-13-2009] Avira Antivir ZIP evasion - BID34723
- [TZO-11-2009] Fortinet - Generic evasion (Limited details) - BID34583
- [TZO-10-2009] Nod32 - Generic evasion (Limited details) - BID34764
- [TZO-09-2009] Avast! - Generic evasion (Limited details) - BID34578
- [TZO-08-2009] Bitdefender - Generic evasion (Limited details) - BID34580
- [TZO-07-2009] F-Prot - ZIP Method evasion - BID15293 - CVE
- [TZO-06-2009] IBM Proventia - Generic evasion (Limited disclosure)
- [TZO-05-2009] ClamAV below 0.95 - Generic evasion (Limited disclosure) - BID34344
Hardware
I am by far not an electronic engineer - I learned to solder and modified a bit of hardware as a hobby and out of interest.
This is my version of the the Bluetooth Sniper weapon, it features a medium sized YAGI antenna combined with a 10* magnification scope and a metalized parabolic which may bundle the Bluetooth signal, thus further enhancing the range.A long term project with regards to USB devices and security.



.png)




.png)
0 comments
Post a Comment