 Hmm, I see a very clear trend of marketing entering the security process, sorry let me rephrase that, it's not a trend - it's there.
Hmm, I see a very clear trend of marketing entering the security process, sorry let me rephrase that, it's not a trend - it's there.
There is a clear indication that vulnerability counts have to be kept low as possible - especially in competitive markets like AV and browsers.
The movements go as far as denying DoS to be a security issue, the reason given : there are so many of them - I am not kidding.
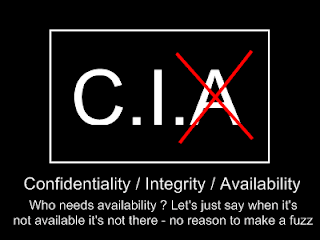
What the hell ? Denial of Service is a vulnerability per se. There is simply no discussion about it, it's the A in C.I.A. What you should measure is the Impact. If the vendor assess the the impact as being very low for their customers I have nothing against being told so and I simply make it clear in the advisory, however trying to tell me that remotely affecting the availability of an application does not affect security - is a joke.
The impact is what should be measured by vendors, make it very clear to your customers what the impact is, so your customers can make a concise risk decision on whether to patch or not, whether to mitigate or not.
The problem is, it doesn't look very good in vulnerability statistics, more and more products are regularly compared to how they perform on the "how many advisories for each product" and vendors are actively trying to keep that number as low as possible - responsibility ? my buttock.
From the 800 vulnerability notifications I send in the last 2 years, 3 (!) were published by vendors voluntarily, you would think that if they care about the security of their clients they would even if it's just due diligence advise their clients of security problems that were fixed - no, nada, niente. Out of those 3 advisories, one vendor choose to centralise 8 distinctive vulnerabilities into one advisory. The effect? In the vulnerability statistics you see on-line it will look as ONE bug. nice, responsible and fair. dream on.
Under the umbrella of responsible disclosure "we" security researches are playing the ball game. If you didn't know yet, instead of fighting with vendors over stupid bugs, lots of them sell the vulnerabilities, not only don't they have to deal with lengthy frustrating e-mails trying to help the vendor (for free), they even get paid to have found the problem.
The downside is that this is less responsible since you are telling a third party particular interesting information. (That mostly all sell it to interesting three letter agencies behind the back, while customers are waiting months to years for a patch).
The fact is that the most prominent and dominant security researchers have been bought, they either get regular contracts at those companies or directly work in their offices - vulns are silently handed over - payback time is another project, not officially of course. Manus manum lavat. Responsibility ? My buttock.
Here is an example of the Denial of Service is not a security vulnerability paradigm, the company in question will not be named yet (wait for the advisory) :
1. Report a remote DoS condition in Product X to Comp. Inc.
2. Report a second remote DoS condition in Product Y to Comp. Inc
3. Report a remote DoS condition in a Product where the market is more competitive to Comp. inc (NB same company)
Now what is it for Comp. Inc. ? Has Denial of Service now been spontanously been promoted to very important ? Or is it just that this makes them look bad in face of the competition. My answer to that company, was that they have to make a choice, either DoS is a security problem or it's not, I will respond accordingly and publish.
Some backround :
1 - Been reporting a (simple) browser bug - resulting in various DoS conditions
2 - I have been met with some of the most astounding reactions I have ever had


.png)

.png)


0 comments
Post a Comment