The responsibilities of vendors, suppliers, and service providers have grown increasingly important in the dynamic digital economy. The growing digitalisation and reliance on third-party entities significantly enhances business operations while concurrently introducing a spectrum of security risks.
Recognising these challenges, regulatory supervisors have been actively creating frameworks over the years to make sure that financial entities in particular appropriately handle and mitigate the risks of security incidents that could directly affect their operations.
The adoption of specific guidelines by the European Banking Authority (EBA) in marked a substantial acceleration of the shift towards a more security-conscious approach when interacting with third parties. These guidelines were a significant advancement in highlighting the important security aspects to take into account while working with third parties.
However, with the recent final Regulatory Standards published, the Digital Operational Resilience Act (DORA) is further evolving the requirements and expectations in light of multiple high-profile breaches involving third parties and the supply chain. The entry into force of this European Regulation, which takes effect in January 2025, marks the beginning of a new era in third party security management.
It signals a time when strict compliance and proactive risk management are more important than ever in third-party contacts, and it also emphasises the significance of operational resilience and indicates a heightened response to the changing threat landscape.
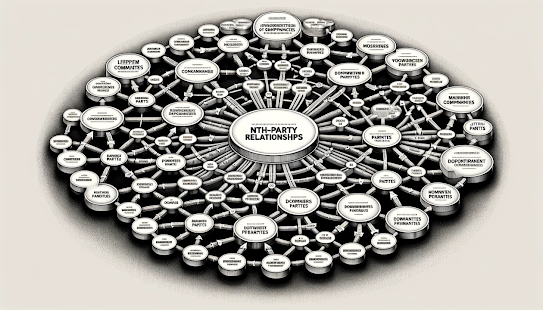
While researching the state of the Art in "Third Party" risk management I came across an Report recently published by Wade Baker, Ph.D. and the Cyentia Institute titled “Risk to the Nth-Party Degree: Parsing the Tangled Web".
In true Cyentia Institute fashion the report is a data driven and provides plenty of opportunity for the data science geeks amongst us to rejoice - for the others it's one of the first publicly available reports providing us with data analysis on the matter with.
The Report highlights a crucial aspect that is often overlooked in risk management: vendor risk extends beyond direct third parties.

.png)



_(thousands)_RYB2016.png)





